Under the guidance of a mysterious man called "The Professor", a group of robbers, Tokyo, Rio, Berlin, Nairobi, Denver, Moscow, Oslo, and Helsinki, invade the Royal Mint of Spain and take hold of 67 hostages as part of their plan to print, and escape with, €2.4 billion. Raquel Murillo, a police investigator is put in charge of the case, unaware that the mastermind is closer than she could ever imagine.
Un enigmático hombre que se presenta como “el profesor” forma un equipo con 8 ladrones con el propósito de dar el mayor golpe de la historia con un atraco a la Fábrica de moneda y timbre. El equipo se instala en la fábrica secuestrando 67 rehenes y comienza a imprimir dinero. Raquel Murillo, la inspectora puesta a cargo del caso, no sabe que el cerebro detrás del atraco está más cerca de lo que se podrá imaginar.
Establishing a way back into the system (e.g., creating a new user or a cron job).
Using the compromised machine to attack other systems on the internal network that weren't previously accessible. 6. Reporting
The go-to tool for executing exploits. Use msfconsole to search, configure, and launch attacks.
Use Whois , Nslookup , and theHarvester to find domain ownership, IP ranges, and employee emails without touching the target's servers. Active Recon: Use Nmap to discover open ports and services.
Moving from a low-level user to Root or SYSTEM . Tools like LinPEAS or WinPEAS automate the search for misconfigurations.
This is the "hacking" phase where you bypass security controls.
High-level risks for non-technical stakeholders.
Example: nmap -sV -O [target_ip] (Identifies service versions and the operating system). 3. Vulnerability Analysis Once you know what’s running, find the "holes."
Binge watching the latest season of a great TV show is everyone's guilty pleasure. But we just can’t seem to find 1 hour per week to dedicate to our Spanish studies. Now imagine a world where you could learn Spanish just by watching great Spanish TV shows. Well that’s exactly “The Binge Learning Method by Lingopie.”
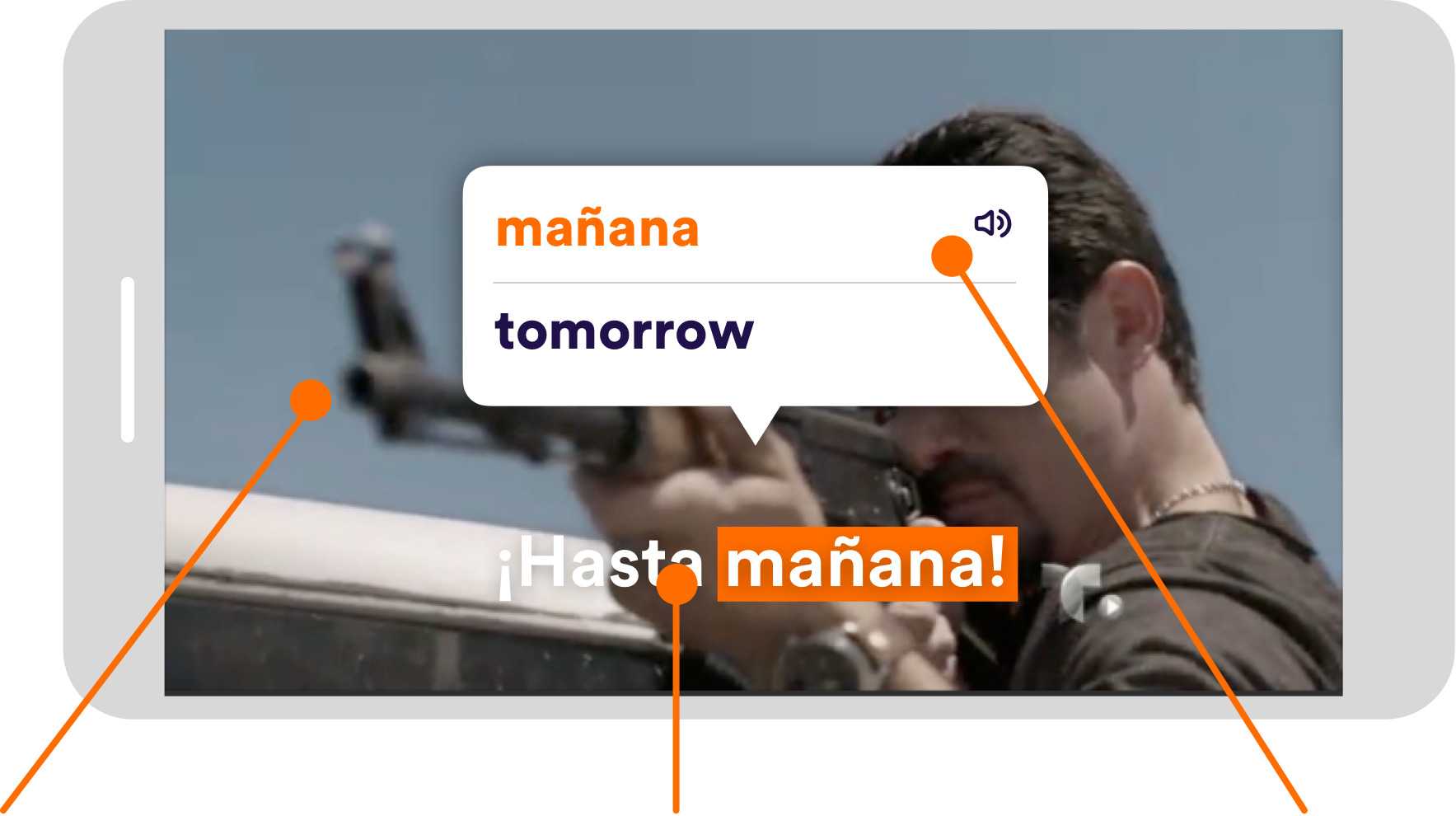
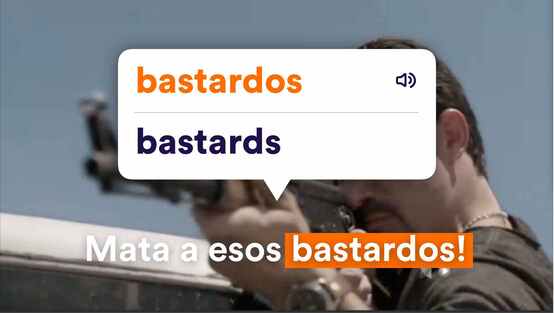
Choose a great Spanish TV show from our extensive catalog of TV Shows. Each Spanish TV show is displayed with Spanish subtitles. Start watching and when you don’t understand something, just click on that word or phrase and get an instant translation. Lingopie saves all your words and phrases so you can review them afterwards with built-in SRS language learning tools. As you binge watch from episode to episode, you’ll quickly notice that you understand more & more in record time. The more you watch, the more you learn. That’s the “Binge Learning Method.”
LingoPie makes learning addictive! Using interactive closed captions and
great foriegn contnent, learning a new language is as fun as watching TV.


and dozens of other great shows!
Enjoy Great Shows
Highly acclaimed
Spanish TV shows
Click & Translate
Interactive, clickable,
same language captions
Learn From Context
Contextual translations,
grammar and sample sentence
Highly acclaimed Spanish TV shows.
Interactive, clickable, same
language captions
Contextual translations, grammar and
sample sentence
Establishing a way back into the system (e.g., creating a new user or a cron job).
Using the compromised machine to attack other systems on the internal network that weren't previously accessible. 6. Reporting
The go-to tool for executing exploits. Use msfconsole to search, configure, and launch attacks.
Use Whois , Nslookup , and theHarvester to find domain ownership, IP ranges, and employee emails without touching the target's servers. Active Recon: Use Nmap to discover open ports and services.
Moving from a low-level user to Root or SYSTEM . Tools like LinPEAS or WinPEAS automate the search for misconfigurations.
This is the "hacking" phase where you bypass security controls.
High-level risks for non-technical stakeholders.
Example: nmap -sV -O [target_ip] (Identifies service versions and the operating system). 3. Vulnerability Analysis Once you know what’s running, find the "holes."